Microsoft Sentinel REST APIs vs MS Graph
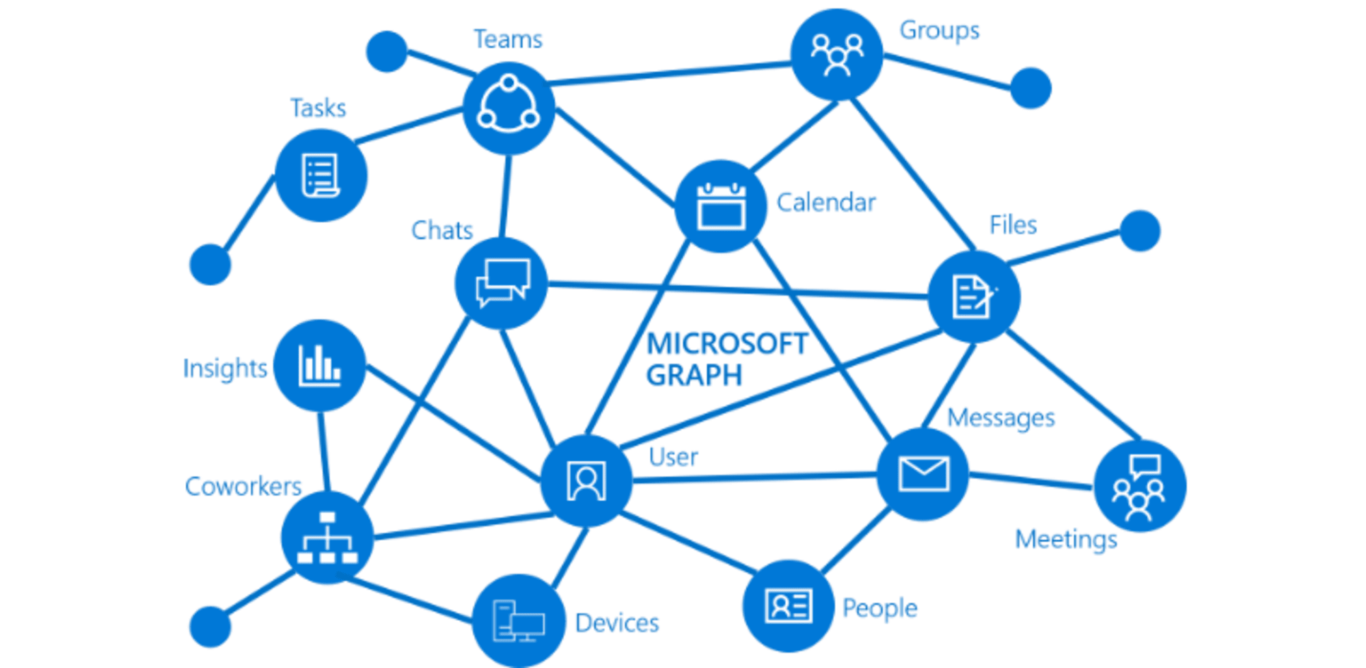
Introduction If you have connected your Microsoft Sentinel instance to your Microsoft Defender instance (and if not, why not?), you know that the same incidents and alerts will show up in both instances. You can use either the Microsoft Sentinel REST API or the MS Graph to get the data. So, which one should it […]